Data breaches climbed to a record high in 2025. How to protect your personal information
Data breaches climbed to a record high in 2025. How to protect your personal information
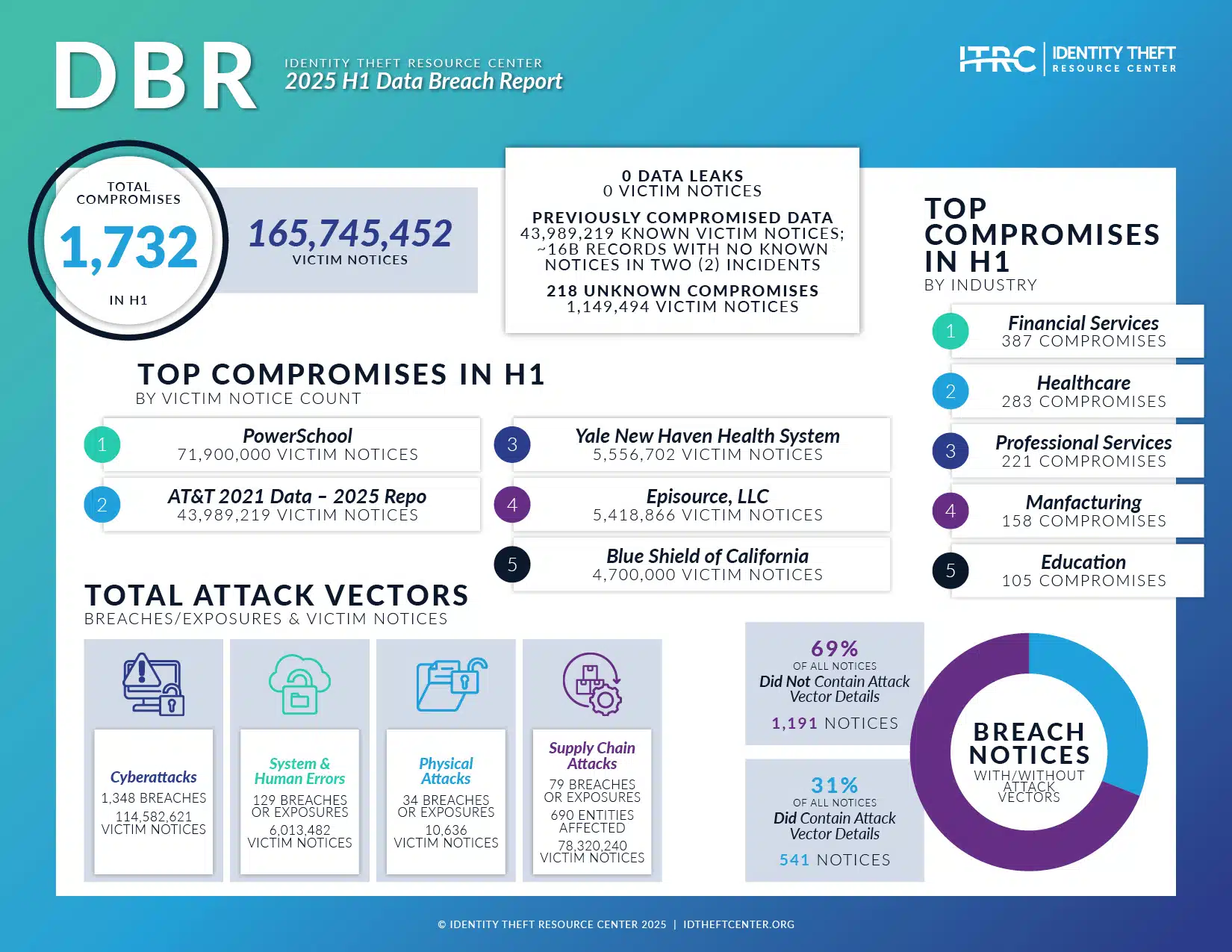
The numbers are terrifying, yet predictable. In 2025, global data breaches reached an unprecedented peak, shattering previous records set during the rapid digitalization of the early 2020s. Millions of user records—from financial credentials to highly sensitive medical data—were exposed in what cybersecurity experts are now calling the 'Great Digital Spill.' If you haven't received a breach notification yet, statistics suggest it's only a matter of time.
I remember the sinking feeling when my bank notified me last March. It wasn't just a generic email; it was confirmation that my date of birth, mother's maiden name, and previous address were floating around the dark web. The realization was stark: our personal data is no longer safe behind simple passwords. It is the new oil for organized cybercrime syndicates.
This escalating crisis demands immediate, proactive change in how we manage our digital lives. Protecting your identity and financial stability in this new hyper-vulnerable landscape requires moving beyond basic antivirus software. It requires developing robust, resilient digital hygiene habits.
The Anatomy of the 2025 Cyber Tsunami
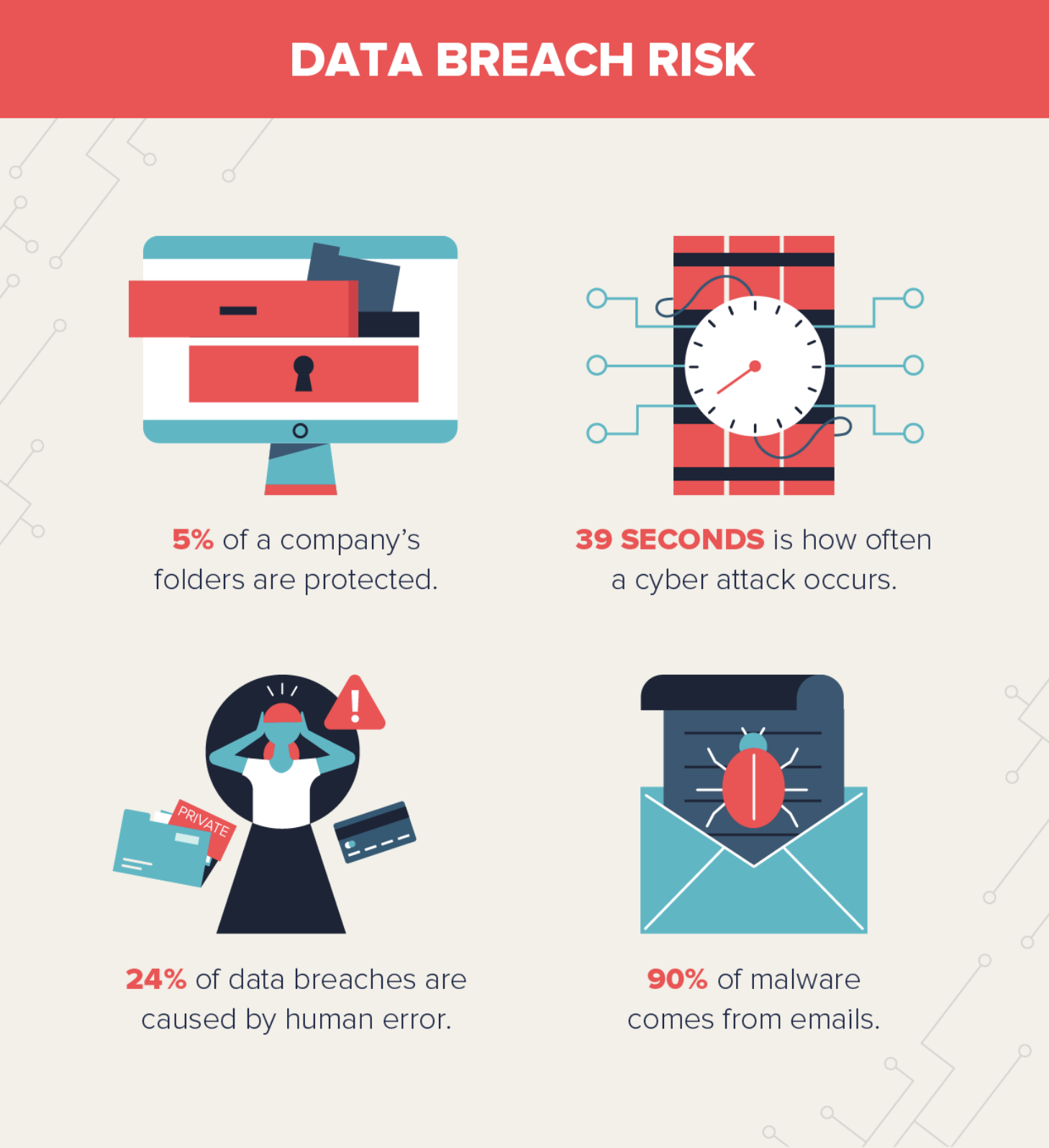
What drove the steep increase in data breaches this year? While human error remains a consistent factor, the primary catalyst was the maturity and widespread deployment of Artificial Intelligence (AI) by malicious actors. Sophisticated AI tools allowed hackers to scale their attacks and bypass legacy security systems with alarming efficiency.
AI-enhanced phishing campaigns, for example, became virtually undetectable, generating hyper-personalized emails and deepfake voice calls that tricked even cautious users into handing over credentials. Furthermore, the proliferation of Internet of Things (IoT) devices in homes and businesses created thousands of new attack vectors that were poorly secured.
The healthcare and financial sectors bore the brunt of these attacks, frequently targeted for the sheer volume and value of the sensitive personal information they hold. Ransomware attacks against critical infrastructure also intensified, often resulting in widespread service outages and subsequent data leaks when companies refused to pay the extortionists.
The key takeaway from the 2025 data crisis is clear: the threat environment has evolved faster than standard security protocols. We must adapt quickly to mitigate the risk of identity theft and severe financial loss.
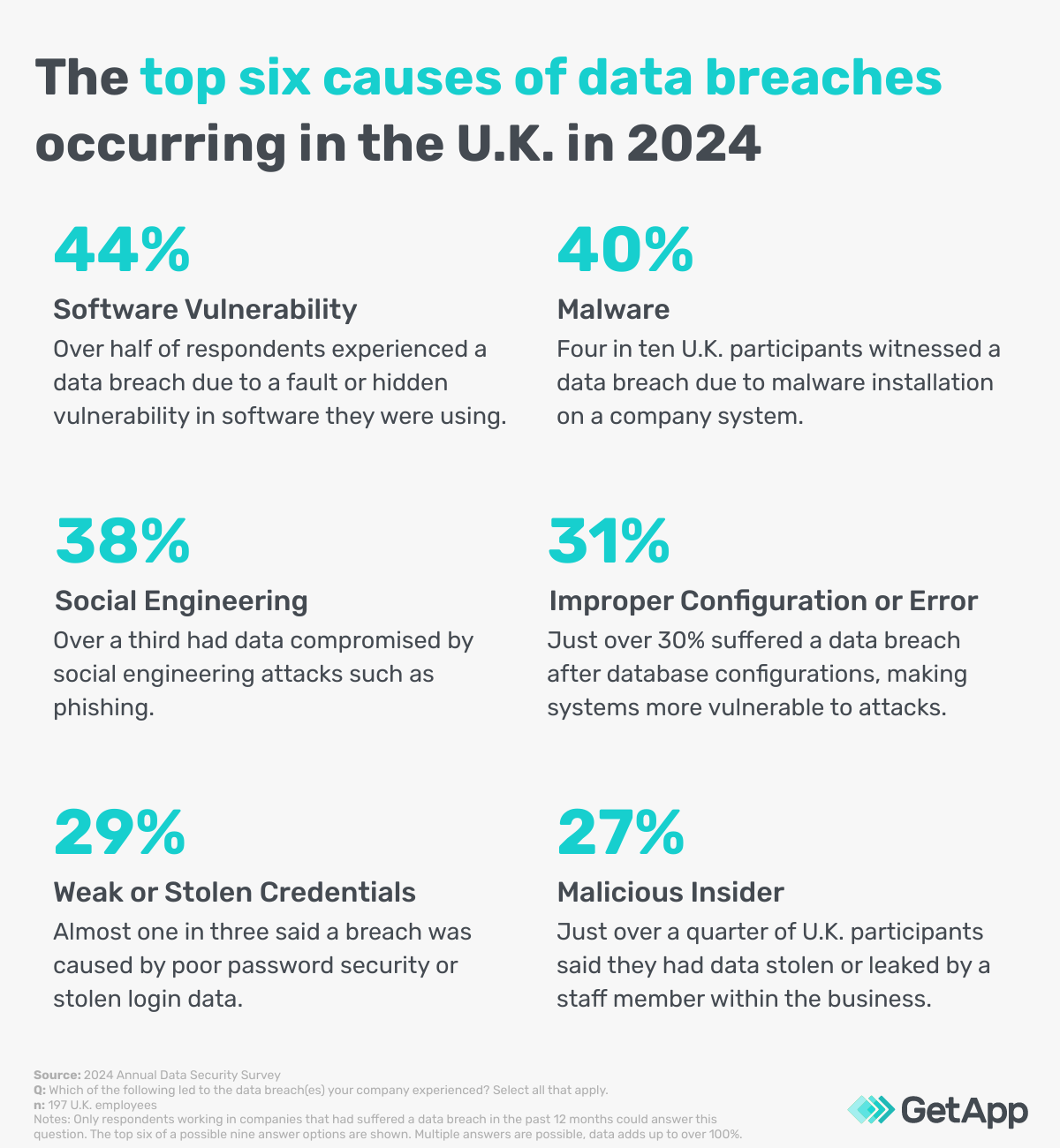
Here are the common vectors contributing to the record breach numbers:
- Supply Chain Vulnerabilities: Hacking one small, unsecured vendor to gain access to a larger, more secure primary company.
- Cloud Misconfigurations: Data stored in the cloud was often left unintentionally exposed due to administrative errors or poor setup practices.
- Zero-Day Exploits: Attackers capitalizing on software vulnerabilities before the vendor has time to release a patch.
- Credential Stuffing: Using passwords leaked from one breach to try accessing hundreds of other accounts linked to the same email address.
Immediate Action: What to Do After a Data Exposure Notification
Receiving an email confirming that your data was involved in a major breach is stressful, but panic is not a strategy. Quick, decisive action is essential to limit potential damage. Treat this notification as a red alert, not just a minor inconvenience.
The moment you receive official confirmation of a data exposure, follow these steps immediately:
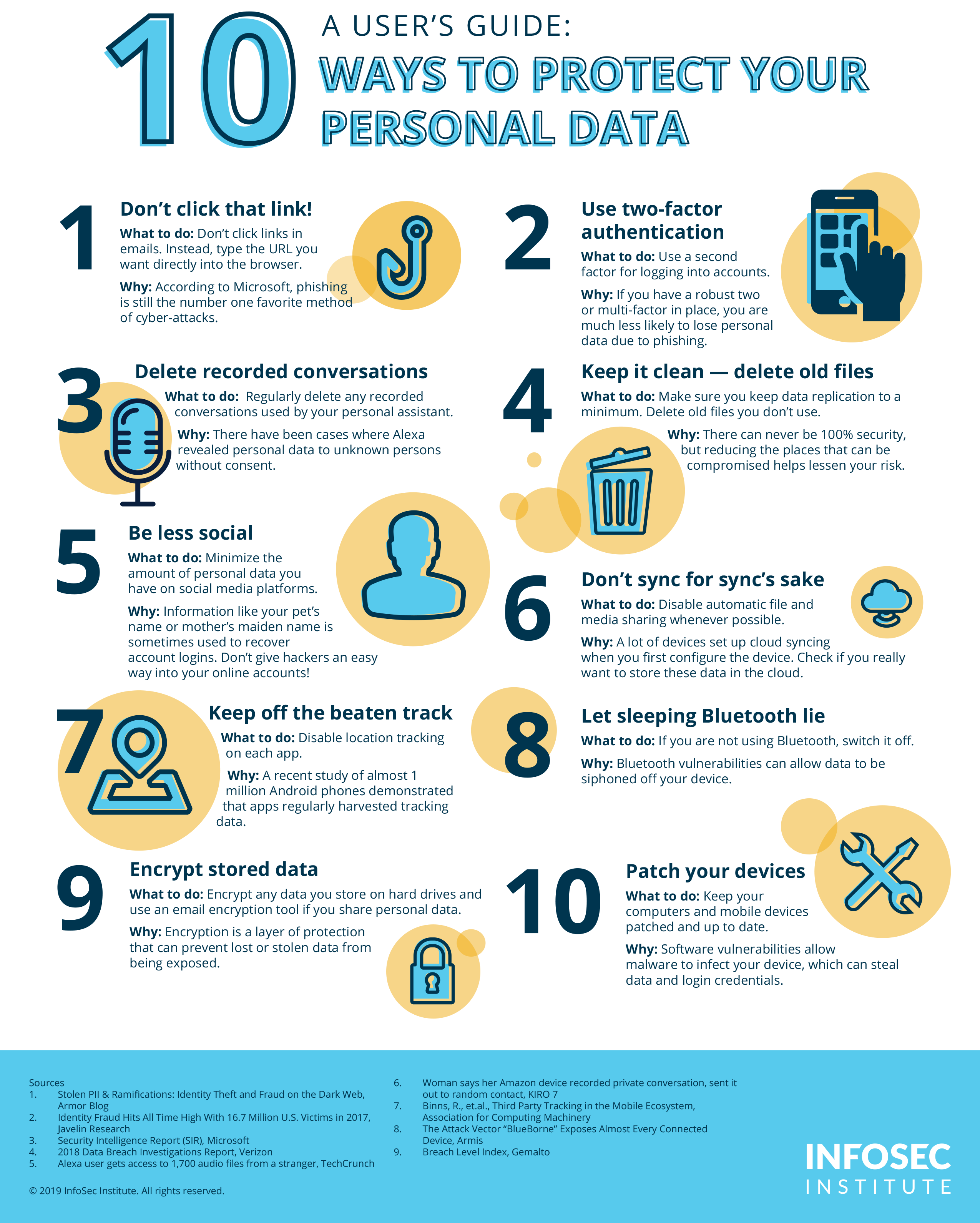
1. Change Passwords—Immediately and Completely
Do not just change the password for the service that was breached. Assume that if your login details were exposed, any site using the same combination is compromised. Use a reputable password manager to generate entirely new, complex, and unique passwords for your banking, email, and primary e-commerce accounts.
2. Activate Multi-Factor Authentication (MFA) Everywhere
MFA (also known as two-factor authentication or 2FA) is the most effective single defense against unauthorized access. If a hacker manages to steal your password, MFA stops them cold because they still need the second factor—usually a code sent to your phone or generated by an authentication app.
3. Place a Fraud Alert or Security Freeze
If financial or credit card information was exposed, contact major credit reporting agencies (Experian, TransUnion, Equifax). Placing a fraud alert requires businesses to verify your identity before extending new credit. A security freeze is even stronger, effectively preventing new accounts from being opened in your name.
- Fraud Alert: Requires identity verification; lasts 1 year.
- Security Freeze: Stops all new credit applications; lasts indefinitely until you lift it. This is the recommended protection against identity theft.
4. Review Financial Statements and Credit Reports
Scrutinize every transaction for suspicious activity, even small charges. Cybercriminals often test stolen cards with tiny purchases before attempting major fraud. Check your full credit report to ensure no new, unauthorized accounts have been opened since the breach occurred.
Fortifying Your Digital Walls: Long-Term Protection Strategies
In the aftermath of 2025's record breaches, prevention is paramount. Long-term digital defense requires consistent vigilance and the adoption of professional-grade cybersecurity tools. Think of your digital life as a fortress; you must close every potential gate and reinforce the walls.
Master Password Management and Vaults
The single most common mistake users make is password reuse. A dedicated password manager (like 1Password, LastPass, or Bitwarden) is no longer optional; it is mandatory. These tools encrypt and store all your complex passwords, requiring you to remember only one master key.
- Generate passwords that are at least 16 characters long, containing a mix of cases, numbers, and symbols.
- Never save passwords directly in your web browser, which are often weak targets for malware.
- Regularly check your password manager for duplicate or weak entries.
Elevate Your Authentication Game
While SMS-based MFA is better than nothing, security experts strongly advise moving toward more secure authentication methods. Hackers can often intercept SMS codes (a practice known as SIM swapping).
The strongest options available today are:
- Hardware Security Keys (e.g., YubiKey): A physical USB device required to log in. This is considered the gold standard for high-security accounts.
- Authenticator Apps (e.g., Google Authenticator, Authy): Apps that generate rotating time-based codes, independent of cellular networks.
Beware of Phishing and Social Engineering
Phishing remains the simplest way for hackers to breach defenses, regardless of technical complexity. Assume every unsolicited email, text, or phone call asking for verification or clicking a link is malicious until proven otherwise.
Always verify the sender's email address down to the domain name. If an email claims to be from your bank, navigate directly to the bank's official website rather than clicking the link provided in the message.
Cybersecurity training emphasizes skepticism. If an offer seems too good to be true, or if a notification demands immediate, high-pressure action, it is likely a scam designed to exploit human fear or greed.
Maintain Software and Network Hygiene
Unpatched software is a gaping vulnerability. When companies release security updates, they are fixing known holes. Delaying these updates gives hackers a clear path inside.
- Update Everything: Set your operating system (OS), applications, and even smart devices (routers, smart TVs) to auto-update immediately.
- Use a VPN: Never connect to public Wi-Fi (like coffee shops or airports) without a high-quality Virtual Private Network (VPN). A VPN encrypts your traffic, preventing snoopers from monitoring your activities.
- Review Permissions: Audit the mobile apps and online services that have access to your contacts, camera, or location data. Revoke permissions for services you no longer actively use.
Looking Ahead: The Future of Digital Hygiene
The record high data breaches of 2025 serve as a painful, expensive lesson. As the digital landscape becomes increasingly complex—with generative AI driving both innovation and sophisticated cybercrime—our approach to security must shift from reactive fixes to proactive vigilance.
Embracing a zero-trust mindset is critical. Assume that every network, user, and device is potentially compromised, requiring continuous authentication and verification. This may sound paranoid, but in the current cyber climate, it is simply pragmatic.
Protecting your personal information is an ongoing effort, not a one-time setup. By implementing robust MFA, utilizing dedicated password managers, and maintaining meticulous software hygiene, you can build digital defenses strong enough to weather the next inevitable wave of cyberattacks and secure your identity in the challenging years ahead.
Data breaches climbed to a record high in 2025. How to protect your personal information
Data breaches climbed to a record high in 2025. How to protect your personal information Wallpapers
Collection of data breaches climbed to a record high in 2025. how to protect your personal information wallpapers for your desktop and mobile devices.
Vibrant Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Artwork for Desktop
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Stunning Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture for Desktop
A captivating data breaches climbed to a record high in 2025. how to protect your personal information scene that brings tranquility and beauty to any device.
Dynamic Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture Photography
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.

Artistic Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture in 4K
Find inspiration with this unique data breaches climbed to a record high in 2025. how to protect your personal information illustration, crafted to provide a fresh look for your background.
Spectacular Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information View in 4K
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.
Gorgeous Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Wallpaper in HD
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.

Mesmerizing Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture Art
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Detailed Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Photo Collection
Explore this high-quality data breaches climbed to a record high in 2025. how to protect your personal information image, perfect for enhancing your desktop or mobile wallpaper.
Spectacular Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Capture Collection
Immerse yourself in the stunning details of this beautiful data breaches climbed to a record high in 2025. how to protect your personal information wallpaper, designed for a captivating visual experience.

Breathtaking Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Artwork Illustration
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Mesmerizing Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Scene Collection
Discover an amazing data breaches climbed to a record high in 2025. how to protect your personal information background image, ideal for personalizing your devices with vibrant colors and intricate designs.

Gorgeous Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Moment for Desktop
This gorgeous data breaches climbed to a record high in 2025. how to protect your personal information photo offers a breathtaking view, making it a perfect choice for your next wallpaper.
Mesmerizing Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Design Nature
Transform your screen with this vivid data breaches climbed to a record high in 2025. how to protect your personal information artwork, a true masterpiece of digital design.

Spectacular Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information View Photography
A captivating data breaches climbed to a record high in 2025. how to protect your personal information scene that brings tranquility and beauty to any device.
Vivid Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Moment Illustration
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Breathtaking Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Design Photography
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Gorgeous Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Picture Nature
A captivating data breaches climbed to a record high in 2025. how to protect your personal information scene that brings tranquility and beauty to any device.

Vivid Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Moment Illustration
Transform your screen with this vivid data breaches climbed to a record high in 2025. how to protect your personal information artwork, a true masterpiece of digital design.

Beautiful Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Design Digital Art
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.

Breathtaking Data Breaches Climbed To A Record High In 2025. How To Protect Your Personal Information Artwork for Your Screen
Experience the crisp clarity of this stunning data breaches climbed to a record high in 2025. how to protect your personal information image, available in high resolution for all your screens.
Download these data breaches climbed to a record high in 2025. how to protect your personal information wallpapers for free and use them on your desktop or mobile devices.